Advanced Threat Analytics: How long does it take to get useful data?
Microsoft’s Advanced Threat Analytics – ATA – is a superb security product. but when will you start to get useful data from it?
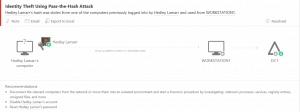
There are two different types of threat detection present in ATA. The first is the detection of suspicious and dangerous activities using deep packet inspection and event log data. Using just this data, ATA detects the following types of security risks as soon as it is active:
- Broken trust
- Weak protocols
- Known protocol vulnerabilities
- Pass-the-Ticket (PtT)
- Pass-the-Hash (PtH)
- Overpass-the-Hash
- Forged PAC (MS14-068)
- Golden Ticket
- Skeleton key malware
- Reconnaissance
- Brute Force
- Remote Execution
Many organizations will see immediate value with the ability to detect and perform further investigations on these activities. ATA reports these and offers guidance on how to deal with each attack.
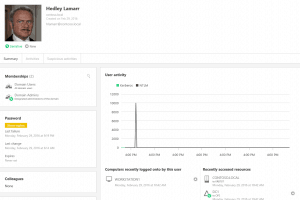
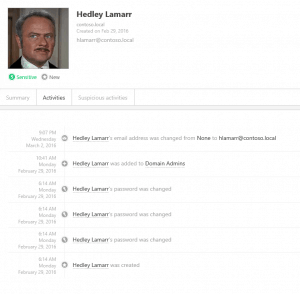
Additionally, you’ll start to see that it identifies sensitive users and starts tracking resources that are accessed by them.
You can even drill down to the user level and get details on user activities.
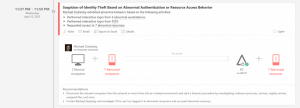
The second type of detection is available after 30 days of data collection. Utilizing behavioral analytics, ATA can detect the following risks:
- Anomalous logins
- Remote execution
- Suspicious activity
- Unknown threats
- Password sharing
- Lateral movement
These events include the same guidance as passed detections but with more data about the threat since it was identified using historical data.
 Both types of detection require minimal configuration and are geared to reduce false positives. Adding ATA to your existing security tools is a very smart move.
Both types of detection require minimal configuration and are geared to reduce false positives. Adding ATA to your existing security tools is a very smart move.