Azure Active Directory SaaS Provisioning
Provisioning Identities to SaaS applications is no longer a laborious task
Attribute Mappings
Just like a MIM management agent Azure AD allows you to configure outbound attribute mappings to SaaS app. These can be viewed after setting up user provisioning in the Azure Portal.
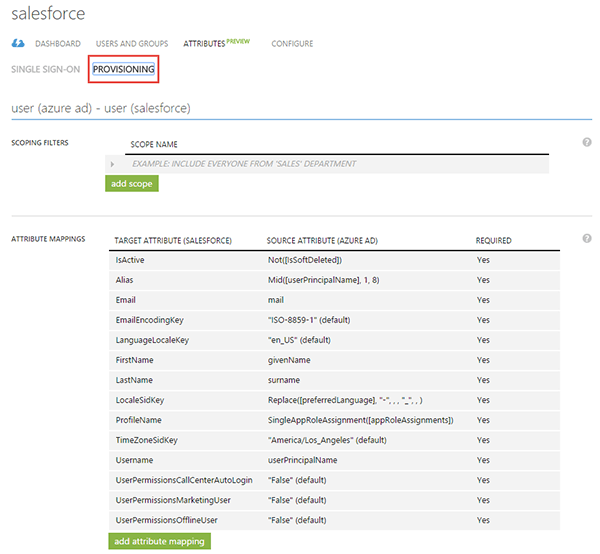
Out of the box the Azure team has already configured basic attribute flows for you. It’s highly recommended not to change these unless completely necessary.
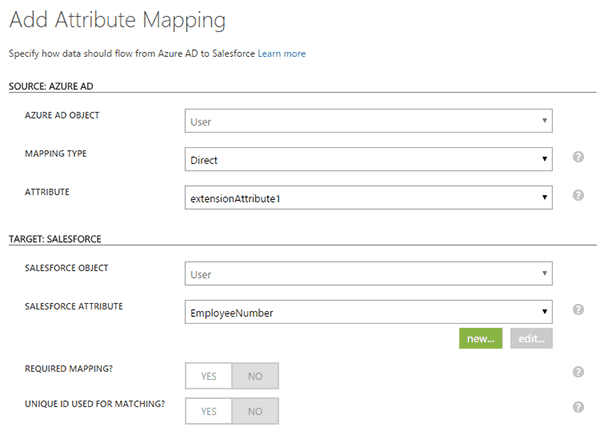
Attribute flows can be added. In my example below I’m mapping extensionAttribute1 to Employee Number in sales force.
More information on attribute mappings can be found here.
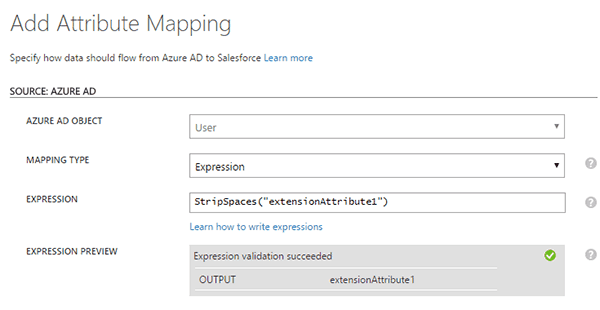
Expressions are also available. In this example I’m striping all spaces from extensionAttribute1 before mapping it to Salesforce Employee Number.
More information on expressions can be found here.
Matching Rules
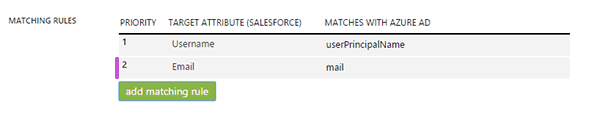
Tucked away at the bottom of the provisioning attributes page are the matching rules. These are the equivalent to join rules in FIM/MIM.
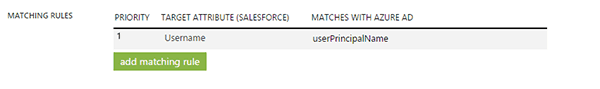
Similar to attribute mappings the Azure team has added a rule to match AAD userPrincipalName to Salesforce Username. This can be modified or you can add additional mapping rules which are ranked in order of priority.
In my example below I’ve added a matching rule to look for a match between email address and the mail attribute in Salesforce.
That’s the basics of attribute mappings and matching rules. Please read my next blog on provisioning behavior.