Azure AD B2B collaboration
One of the new things in the Azure Active Directory (AD) identity space is Business to Business collaborations, and adds to your Azure AD. Azure AD has excellent SaaS application integration. In this post, find out how you can provide access to those applications to external B2B partners.
Here’s how Azure AD B2B works
Use Cases
Azure B2B is great for providing external partners with access to your organizations cloud applications and resources.
Get Ready…..Build your CSV
Your CSV must be less than 2,000 rows, but you can upload multiple CSVs
Required Fields:
Email: Email address for invited user.
DisplayName: Display name for invited user (typically, first and last name).
InviteContactUsUrl: “Contact Us” URL to include in email invitations in case the invited user wants to contact your organization.
Optional Fields:
InviteAppID: The ID for the application to use for branding the email invite and acceptance pages. The IDs can be retrieved using the cmdlet: Get-MsolServicePrincipal | fl DisplayName, AppPrincipalId
InviteAppResources: AppIDs to which applications can assign users. AppIDs are retrievable by calling Get-MsolServicePrincipal | fl DisplayName, AppPrincipalId
InviteGroupResources: ObjectIDs for groups to add user to. ObjectIDs are retrievable by calling Get-MsolGroup | fl DisplayName, ObjectId
InviteReplyURL: URL to which to direct an invited user after invite acceptance. This should be a company-specific URL (such as contoso.my.salesforce.com). If this optional field is not specified, the inviting company’s Access Panel URL is generated (this URL is of the form https://account.activedirectory.windowsazure.com/applications/default.aspx?tenantId=TenantID
Language:
Language for invitation email and redemption experience, with English as the default when unspecified. The other 10 supported language codes are:
- de: German
- es: Spanish
- fr: French
- it: Italian
- ja: Japanese
- ko: Korean
- pt-BR: Portuguese (Brazil)
- ru: Russian
- zh-HANS: Simplified Chinese
- zh-HANT: Traditional Chinese
Uploading and sending invites
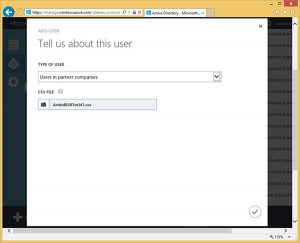
In the azure portal you’ll want to navigate to your Azure AD where these user objects will reside and require application access. Click add user and choose Users in partner companies from the type of user drop down. Browse for the CSV and you’re off!
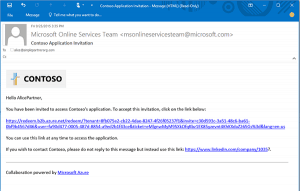
Once uploaded the users in the CSV will receive an email like this:
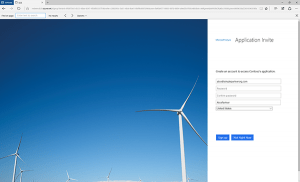
and then be directed to an account claim page:
They will then be sent to the My Apps portal where they can access the applications they were granted access.
Limitations
- Multi-factor authentication (MFA) not supported on external users.
- Invites are possible only via CSV; individual invites and API access are not supported.
- Only Azure AD Global Administrators can upload .csv files.
- Invitations to consumer email addresses (such as hotmail.com, Gmail.com, or comcast.net) are currently not supported.
- External user access to on-premises applications not tested.
- External users are not automatically cleaned up when the actual user is deleted from their directory.
- Invitations to DLs are not supported.
- Maximum of 2,000 records can be uploaded via CSV.
How to automate this
Currently there doesn’t appear to be a way to automate this process. However with Microsoft Identity Manager and a couple of custom workflows, the CSV could be built based upon a user request and then sent to an admin to upload the CSV to Azure AD.