Supercharge Azure RMS with Azure Information Protection
Azure Information protection adds highly anticipated features for controlling your organization’s data
In my other posts about Azure RMS (here) we looked at how to apply protection to documents in your organization. With the integration of RMS with Exchange, SharePoint, and FCI there still can be gaps with content that users create on their workstations. The release of Azure Information Protection fills in that gap.
A client must be installed on the user’s workstation and in the same manner the RMS share protected add-in integrates with Microsoft Office. It’s compatible with Office 2010, 2013, and 2016.
You can download the Azure Information Protection Public Preview here. Once installed, when the user opens an Office application they will have to sign in for the service to operate.
Once installed, a sensitivity bar is visible in Office documents.
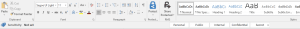
With this bar a user can classify content with the tags that they feel meet the criteria for the content they are creating.
While users can classify their content, the power behind this product comes from the settings in the Azure portal.
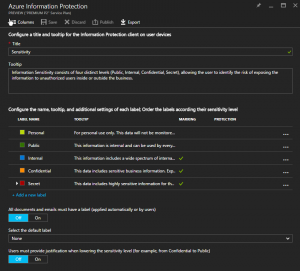
Each content sensitivity label and tooltip can be customized to fit your organization’s needs. Additionally, you can require that documents need a label and justification when lowering the sensitivity.
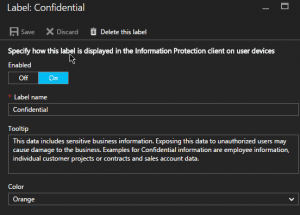
Each sensitivity label has its own settings.
The label name correlates to the sensitivity level in Office applications. Tooltips are displayed to end users when hovering over a sensitivity label.
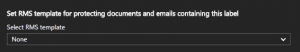
The ability to apply RMS templates via a sensitivity label is what makes this update so compelling. When this is set up, each document with the sensitivity label is protected with RMS encryption and permissions.
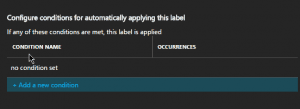
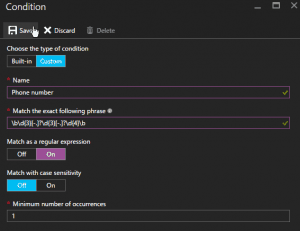
Sensitivity labels can also be applied if certain conditions are met in the document. Microsoft has included some built-in criteria focusing on financial and personal information detection.
If desired, you can create your own criteria. You can either look for exact text strings or use regular expressions. This is my favorite RegEx testing site.
Deploying changes to the clients in your organization is performed by using the publish button in the portal. This is similar to Azure RMS templates where the template is not available until published. This allows administrators to make changes to their Azure Information Protection settings but not alter the user experience until ready to go live.
Azure Information Protection offers your organization the ability to classify and protect content regardless of where the user is saving and working on the content.
More information here.